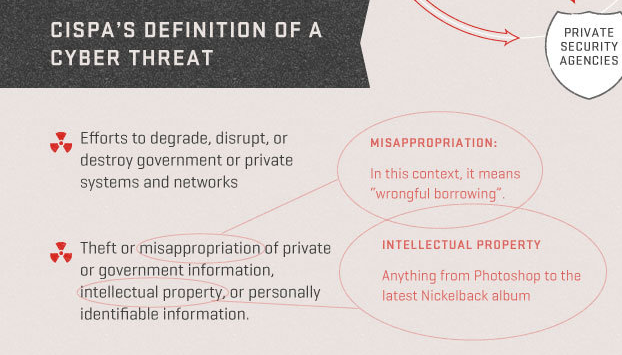
Here’s the key point from the EFF’s simple outline of the provisions of CISPA, the latest attempt to turn file sharers into terrorists. Here’s the ACLU’s take on new amendments to the bill, and an ACLU memo on different cybersecurity measures that will be debated in Congress in the next few weeks.
CISPA
by $8 blue check mistermix| 57 Comments
This post is in: Ever Get The Feeling You've Been Cheated?

burnspbesq
There is no problem in IP law and related disciplines that Congress can’t make worse by trying to fix it.
Villago Delenda Est
Can we include “daring to question corporate overlords online” as one of the dire threats?
piratedan
the spice must flow!!!!!!!!!!!!!!!!!!!!!!!!!!!
Villago Delenda Est
Wouldn’t an effort to “destroy” government or private networks be more in the realm of actual physical attacks on infrastructure? Wouldn’t that be something other than a “cyberthreat”, which implies a virtualness to it, as in an DOS attack or attempting via exploits to disrupt networks?
These morons have no fucking idea what they’re talking about. I’ll betcha the fascist pigshit of ALEC is involved in this.
gaz
I didn’t stop hacking shit when they called me a terrorist.
And I certainly am not going to stop using file-sharing.
* adjusts suicide vest *
Matoko Borgia-Steeler
@gaz:
I shall wear my Rachel Ray terrorist file-sharing jihadi scarf with pride. Soil yourself with terror, Michelle Malkin!
Baud
However one feels about copyright protection/file sharing, I don’t think it falls under the rubric of “cybersecurity.”
Ben Franklin
https://torrentfreak.com/megaupload-trial-may-never-happen-judge-says-120420/
A US judge has put a bomb under the Megaupload case by informing the FBI that a trial in the United States may never happen. The cyberlocker was never formally served with the appropriate paperwork by the US authorities, as it is impossible to serve a foreign company with criminal charges.
I think The Feds are smart enough to have known this.
kdaug
Do love the little radiation symbol bulletpoints on the list, though.
“If you share files, your hair will fall out and you will hemorrhage!”
Cap'n Magic
Now that the MegaUpload trial may never happen, you can bet the MPAA, RIAA, and the network security infrastructure industry will pull all stops to back this latest piece of offal.
Corner Stone
Speaking of file sharing, was this previously mentioned?
Dotcom trial may not occur – Judge
“The criminal charges against Kim Dotcom in the United States may never get to trial, the judge overseeing the case has told the FBI.
United States district court judge Liam O’Grady said he didn’t know if “we are ever going to have a trial in this matter” after being told Dotcom’s file-sharing company had never been formally served with criminal papers by the US.”
ETA, ok, talk about getting taken to the woodshed…
Corner Stone
@Ben Franklin: Speaking of FCPA, which we were in the Wal Mart thread, it seems our FBI did a little of the business for the Big Entertainment Industry by shutting down the site.
Cap'n Magic
@Corner Stone: Yep. Mentioned in a previous Open Thread.
gaz
@Matoko Borgia-Steeler: lol
Ben Franklin
@Corner Stone:
Copyright is just cover for the over-arching agenda. They hate anything they can’t control.
They don’t want the messy international red-tape, so prosecutions after-the-fact should be avoided. They want to shutthe barn door before the horse escapes.
The goal is more pre-emptive.
Ben Franklin
@Cap’n Magic:
I recall mentioning it, but no discussion ensued.
MikeTheZ
Its SOPA all over again. Leaves me with just one thought;
*sigh*
bemused senior
I agree that the CISPA as written is too broad in some regards, but recognize that at the moment, companies like Yahoo, Google, etc. can’t share such things as log information and information about compromised accounts derived from evidence of spamming and fraud activity. Yet the people who run botnets and steal, [eta: sell and use] massive files of credentials from poorly secured commercial websites are very difficult to combat with traditional legal means…they are often in other countries, they may be state actors, they use automated changing of domain names in the command and control networks to make the descriptions of activity that occurred in even the recent past irrelevant to their current activity. The goal of sharing such information is to allow automated defenses against this activity.
gaz
@bemused senior: ISPs regularly share information with each other, often for security purposes.
Furthermore, there are organizations like CERT which already do a fine job of helping orgs protect themselves and recover from botnets and other infections. The reason most systems get infected is that the admins are not exercising appropriate and already existing measures that they could use to protect themselves. IOW, 9 times out of 10, orgs get infected because SOMEBODY isn’t doing their job.
CISPA is paying lipservice to providing these protections, but they already exist. Unless CISPA criminalized lazy net-admins, it adds no value in terms of protecting orgs from hack attempts.
gaz
@bemused senior: One more thing:
You can legislate computer security about as effectively as you can legislate morality. Anyone that tells you different is selling something.
bemused senior
@gaz: You are mistaken if you think that this information is shared to the degree that is needed. There is some sharing, but especially with regards to fraud related activity this is fraught with legal issues for the large providers of web mail and shopping. CERT is completely inadequate for rapid response for targets of botnet type attacks. There is a pretty large academic literature on these problems.
Matoko Borgia-Steeler
@bemused senior:
Could you recommend say five recent relevant items in the academic literature?
Ben Franklin
Question….Who said this and when?
“Th[e National Security Agency’s] capability at any time could be turned around on the American people, and no American would have any privacy left, such is the capability to monitor everything: telephone conversations, telegrams, it doesn’t matter. There would be no place to hide. [If a dictator ever took over, the N.S.A.] could enable it to impose total tyranny, and there would be no way to fight back.“
Answer follows;
Ben Franklin
Frank Church——-1975
http://www.nytimes.com/2005/12/25/weekinreview/25bamford.html?_r=1&pagewanted=all
burnspbesq
@Ben Franklin:
The individual defendants are still going down.
gaz
@bemused senior:
1. CERT is inadequate to fix lazy administrators.
2. So is the law.
The problem cannot be solved by the law. It can be solved by due diligence. I take your academic literature and raise you all of the academic literature, and nearly every opinion of every computer security expert you can name.
Edit: Furthermore, private institutions like ISPs do not need legislation to share information. They can do so voluntarily, unless they’ve entered some sort of NDA with a 3rd party. This almost never applies to the precise technical details of an attack. I hope you’re not suggesting that using the law to compel private companies to release more information would be a good idea, because it’s well, not.
Ben Franklin
@burnspbesq:
So, I guess Corporations are not People, after all.
Ben Franklin
@gaz:
Hammers make bad fly swatters.
danielx
Makes you wonder how much the RIAA had to pony up in campaign contributions to get that language inserted, don’t it now?
@Ben Franklin:
Frank Church, and it’s all true. If bad guys of whatever persuasion are serious, they’re back to 1940s-type security or Moscow rules, as in assume that any electronic or telephonic communication is monitored, snail mail also.
uptown
Yep, this will stop those mean hackers dead in their tracks…because they will be laughing too hard. This is aimed solely at the average consumer.
How about a law that holds corporations and government agencies responsible for keeping their networks/data secure at current standards?
Corner Stone
@danielx:
Think that horse has long left the barn. And we can argue the relative “bad guy-ness” of this administration and previous others, but there’s no doubt we’re in this stage of data sweeping.
bemused senior
@Matoko Borgia-Steeler: Took me a while to narrow this down. I think there are lot of relevant papers in the proceedings from the 2011 BADGER conference. Here is a link to the proceedings. http://iseclab.org/badgers2011/badgers2011-proceedings.pdf
See especially the paper on legal issues.
Public comment on an effort to come up with voluntary ISP practices against botnets are here: http://www.nist.gov/itl/botnetcomments.cfm
The EFF comments address what is problematic in efforts to address botnets.
Quite a bit of the frank discussion about the information sharing between large providers occurs behind closed doors (e.g. MAAWG).
A book that you might find interesting to understand the cross-national issues around prosecuting computer fraud is Fatal System Error by Joseph Menn. Not academic, but imho pretty accurate.
uptown
CISPA will also make it easier to prosecute potential whistle-blowers and make it very difficult for the media to do investigative journalism.
AA+ Bonds
Well this corresponds perfectly to information assurance literature
Although of course that business is not really concerned with the First Amendment
AA+ Bonds
@uptown:
UNFUNDED MANDATE ~(entire country burns down)~
AA+ Bonds
@gaz:
Thanks for posting this, I really wish people would remember that
AA+ Bonds
@bemused senior:
emphasis mine . . . whenever I read something like this the hair on the back of my neck goes up
Bago
If anything, there needs to be a commercially implemented standard for DNSSEC, and propagation policies. That and making sure browsers don’t block on DNS lookups. Sweet hair braids McChrist, waiting for a page to do DNS resolution on all of its CSS and JavaScript files, in addition to the ads. The friggin tracking pixel will add 2 seconds to the page load time. HOOOOOOOOOOOOORJ!
/nerdrage
gaz
As far as a general thought on this kind of legislation. This legislation attempts to fix something that isn’t * particularly * broken.
Hacking happens. Gmail, Sony, et al have experienced it. MS has.
But for all of that, it’s not a crises. It’s cost of doing business. In retail you have “shrinkage”. In IT you have hacks and fraud.
This kind of legislation seeks to solve a problem that it cannot solve. This legislation speaks to the kind of pie in the sky vision of total security, which is basically a digital equivalent of arguing that we should have cameras on everyone so nobody gets mugged. Not only will it not stop the muggings, but…
It’s crazy talk, and the kind of scare tactic regularly employed by politicians operating in a democratic society to backdoor you into giving up some of your rights in the interest of hanging on to as much power and money as they can get. It’s that simple.
Bago
@Villago Delenda Est: Uhhhhm, no. TCP was built with redundancy in mind. Cloud solutions have fault domains to spread the risk around. At Microsoft, we lost the whole Kawajima data center, and kept on trucking.
gaz
@Bago: Yep. =)
Bago
@AA+ Bonds: I helped bust the GNIDA network, and they used default passwords and clear text for their account data, including passwords. Sweet alpha Jesus, how could you try and be clever with blacklists and still be so stupid?
gaz
@Baud:
IT stands for information technology, and thus revolves around intellectual property. It’s part of the game.
The reason I’ve taken on the IT angle is because IP is now being used to regulate IT. It was bound to happen, and I think it’s dangerous NOT to consider them intrinsically linked. I try to make a point to read IP legislation with an eye towards it’s ramifications on IT. I learned that lesson back when IBM fought for patent protection for software – and won – it’s all been downhill from there ;)
gaz
@Bago: been there. seen that ;)
many times.more often than not* sigh *
Bago
When will people realize that on any packet switched network data will be copied, thus making copyright, the right to copy a bit awkward.
gaz
@gaz: OT: also, if you ever worked for the IE team over at MS (I don’t expect you to admit it in polite company – heh) – and if that’s your nick in meat-space, and you snowboard a lot – or used to – I may know you. It’s curious, but stranger things have happened.
If so, hai!
If not, someone who works at MS stole your name, or maybe you stole it =)
gaz
@Bago: Pretty much never. This is why we can’t have nice things. =)
Bago
Don’t even get me started on F5 GTMs. One parsing error in the config file THAT THE PARSE COMMAND DETECTS winds up replicating a config that the execution engine will error out upon, THAT THE PARSING ENGINE
CAN DETECT gets replicated all around the globe.
Goddamn that was a long night.
Villago Delenda Est
@Bago:
TCP may have been build with redundancy in mind, but some of the SONET rings aren’t really rings. Because it’s cheaper (as a consequence of the insatiable need for telcos for profit) to lay fiber side by side, some of the rings may be topographically a ring, but physically, they’re side by side in the same conduit. One backhoe and POOF, there goes your “ring”.
I have seen this actually happen in Oregon where a much ballyhooed “ring” was taken out by one backhoe, because it was a ring nominally, not actually.
Villago Delenda Est
@AA+ Bonds:
What we need is an Enabling Act to get past those pesky “traditional legal means”. Due process is so slow and inflexible, you know. We need summary action! Fire up the Einzatzgruppen and Sonderkommando!
Corner Stone
@Villago Delenda Est: I’ve been debating for the last few minutes. Should I go with the “One ring to rule them all” joke, or the obvious “backhoe”?
Sometimes, life is hard.
Anoniminous
Kinda sorry I didn’t IP protect some of the stuff I wrote in 1979, 1980, and 1981. If I had I’d Pwn Teh Internets!
Which brings-up the Oracle/Google court case. I find it vastly amusing – in a Black/Sick Humor way – Ellison is leading the charge against IP violations when Oracle is based on ripping-off E.F. Cobb’s development of the Relational Database Model and Cobb’s employer at the time, IBM.
Bago
@Villago Delenda Est: Unless you sever at the last hop, traffic *should* be able to reroute at the transport layer.
Bago
@Corner Stone: You could combine them into an amazingly sexist joke.
gaz
@Villago Delenda Est: In that event TCP will reroute
Matoko Borgia-Steeler
@bemused senior:
Thank you so much for the references. I’ll check them out and get myself more informed.
LW
It is so very important that we move to stop CISPA asap. We are slipping down a slippery slope towards a police state here and need to keep whatever liberty we can. For those of you that don’t understand the true and urgent need to stop bills like this from being passed, please take a few hours to watch a new and free documentary online called THRIVE. THRIVE outlines everything that is going on in our world behind the scenes and provides clear and tangible solution strategies for everyone! It’s available free from their website: http://www.thrivemovement.com